If you run iTunes, you need to update it.
One final story got left out of my last blog post about Microsoft updates. It's the first link below. If you run IE, PATCH NOW!
There are some additional security patches which may be of minor interest. On Monday, May 14, 2012, I posted a notice that Adobe to patch Illustrator, Photoshop, and Flash Pro CS5.x for free, Well, they have finally issued patched the last member of the three, Flash Pro. Google's Chrome browser got patched again, but since it auto-updates you should already be using this version. If you use WinAmp, you should patch to the latest version. Links are below.
- Bad guys using unpatched Internet Explorer flaw to hack Gmail accounts
Last week, Google warned its users that “state-sponsored attacks” were under way aimed at accessing Gmail accounts. Those targeted saw a message at the top of their Gmail inboxes warning that “state-sponsored attackers may be attempting to compromise your account or computer”.
At the time, Google was mum on the specific exploit, but on Wednesday Microsoft provided details in a security advisory, and they’re not pretty. Google also discussed the exploit in its own blog post.
Cyberscum are taking advantage of an unpatched, zero-day flaw in Windows XP or later to run malicious code on the user’s computer. The code is planted when the user visits a poisoned website using any version of Internet Explorer. The exploit also works through Microsoft Office documents.
This is a silent, drive-by download. If you’re attacked, you may not know it . . . unless you get that cryptic message atop your Gmail inbox.
On Tuesday, Microsoft release some security fixes for Windows, but a patch for this flaw was not included. Don’t think your Windows PC is protected if you conscientiously updated this week. However, Microsoft has released a “Fix It For Me” item that will block the exploit. All Windows users should apply this, even if you don’t use IE or Gmail, but keep in mind it does not fix the underlying flaw in Windows. A future patch – possibly one released before the next Patch Tuesday – will be released for a true fix.
- Apple, Oracle Ship Java Security Updates — Krebs on Security
Wednesday, June 13th, 2012
There must have been some rare planetary alignment yesterday, because the oddest thing happened: Apple and Oracle both shipped software updates for the same Java security flaws on the very same day. ... The update Oracle released yesterday, Java 6 Update 33 and Java 7 Update 5, fixes at least 14 security flaws in the oft-attacked software that is installed on more than three billion devices worldwide. Apple’s Java update brings Java on the Mac to 1.6.0_33, and patches 11 of the 14 security vulnerabilities that Oracle fixed in Tuesday’s release. It’s unclear whether those other three flaws simply don’t exist in the Mac version of Java, but we’ll take progress where we can get it. - ISC Diary | Java 7u5 and 6u33 released
Published: 2012-06-12,
Oracle is releasing Java 7 update 5 and Java 6 update 33 today.Updated after Oracle released the vulnerability details.
- Release notes for 6u33
- Release notes for 7u5
- Downloads
- Advisory (contains their risk matrix)
- More verbose version of their risk matrix
Unfortunately it's all still made to be useless to determine what the problems are with the software and perform your own risk assessments.
Just note there are CVSS scores of 10 in there, and in the past months we saw what slacking on patching Java can do (Ref: the recent Apple Mac OS X malware), so just patch this on a rather urgent time schedule due to lack of detailed descriptions.
Update:
My words above were barely written or I got the notification of Apple that they are releasing Java for OS X 2012-004 and Java for Mac OS X 10.6 Update 9 today as well. This brings them in line with the updates to 1.6.0_33 above as well as implementing the deactivation of the Java browser plugin and Java Web Start if they remain unused for 35 days to Snow Leopard and deactivating the Java browser plugin and Java Web Start if they do not meet the criteria for minimum safe versions (on Both Lion and Snow Leopard.
- Adobe fixes Flash Player for Firefox to stop crashes | Applications - InfoWorld
June 22, 2012
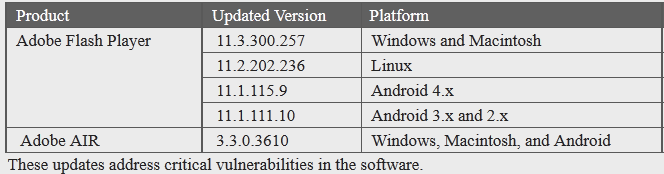
Adobe yesterday updated Flash Player to solve a weeks-long problem for users of Mozilla's Firefox browser.
The update, Flash Player 11.3.300.262, was released Thursday and applies only to Firefox on Windows.
Since Adobe shipped an update to Flash Player to 11.3 two weeks ago, users of Firefox, including older editions as well as the current Firefox 13, had reported crashes when trying to access Flash content.
- Release Notes | Flash Player 11.3 AIR 3.3
June 21, 2012. Welcome to Adobe® Flash Player® 11.3 and AIR® 3.3. This release includes bug fixes related to stability with Firefox on Windows
- ISC Diary | Apple iTunes Security Update
Published: 2012-06-12
Apple announced a new update for iTunes today. Per APPLE-SA-2012-06-11-1, this update addresses a problem when importing a maliciously crafted m3u playlist within iTunes and a problem within WebKit when visiting a maliciously crafted website.
The bulletin is available at http://support.apple.com/kb/HT5318. - About the security content of iTunes 10.6.3
- Adobe - Security Bulletins: APSB12-12 Security bulletin for Adobe Flash Professional
Last Updated: June 25, 2012
Adobe released a security update for Adobe Flash Professional CS5.5 (11.5.1.349 and earlier) for Windows and Macintosh. This update addresses a vulnerability that could allow an attacker who successfully exploits this vulnerability to take control of the affected system. - Chrome 20 fixes 20 security vulnerabilities | ZDNet
By Dancho Danchev | June 27, 2012, 10:59am PDT
Summary: In its latest browser release, 20.0.1132.43, Google’s Chrome fixes 20 security vulnerabilities, none of which are critical. - Winamp 5.63 fixes four critical security vulnerabilities | ZDNet
By Dancho Danchev | June 27, 2012, 10:30am PDT
Summary: Winamp version 5.63 fixes four critical security vulnerabilities.As originally reported in Winamp’s release announcement, version 5.63 fixes four critical security vulnerabilities. Successful exploitation of the vulnerabilities allows execution of arbitrary code. For the exploitation to take place, a user running an outdated version of Winamp, would have to open a specially crafted . AVI video file.
More details about the vulnerability can be found in this Secunia advisory.