Download.com Bundling Toolbars, Trojans? — Krebs on Security
It wasn’t long ago that I felt comfortable recommending CNET‘s download.com as a reputable and trustworthy place to download software. I’d like to take back that advice: CNET increasingly is bundling invasive and annoying browser toolbars with software on its site, even some open-source titles whose distribution licenses prohibit such activity.Although this change started this summer, I only first became aware of it after reading a mailing list posting on Monday by Gordon “Fyodor” Lyon, the software developer behind the ever useful and free Nmap network security scanner. Lyon is upset because download.com, which has long hosted his free software for download without any “extras,” recently began distributing Nmap and many other titles with a “download installer” that bundles in browser toolbars like the Babylon toolbar.
CNET’s own installer is detected by many antivirus products as a Trojan horse, even though the company prefaces each download with the assurance that “CNET hosts this file and has scanned it to ensure it is virus and spyware free.” CNET also has long touted download.com’s zero tolerance policy toward all bundled adware.
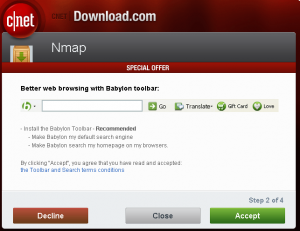
Lyon said he found his software was bundled with the StartNow Toolbar, which is apparently powered by Microsoft‘s “Bing decision engine.” When I grabbed a copy of the Nmap installer from download.com and ran it on a test Windows XP machine, CNET’s installer offered the Babylon Toolbar, which is a translation toolbar that many Internet users have found challenging to remove.
This has also been reported by other security bloggers:



No comments:
Post a Comment